Robust and modern wired and wireless that supports today’s evolving indoor and outdoor connectivity demands.
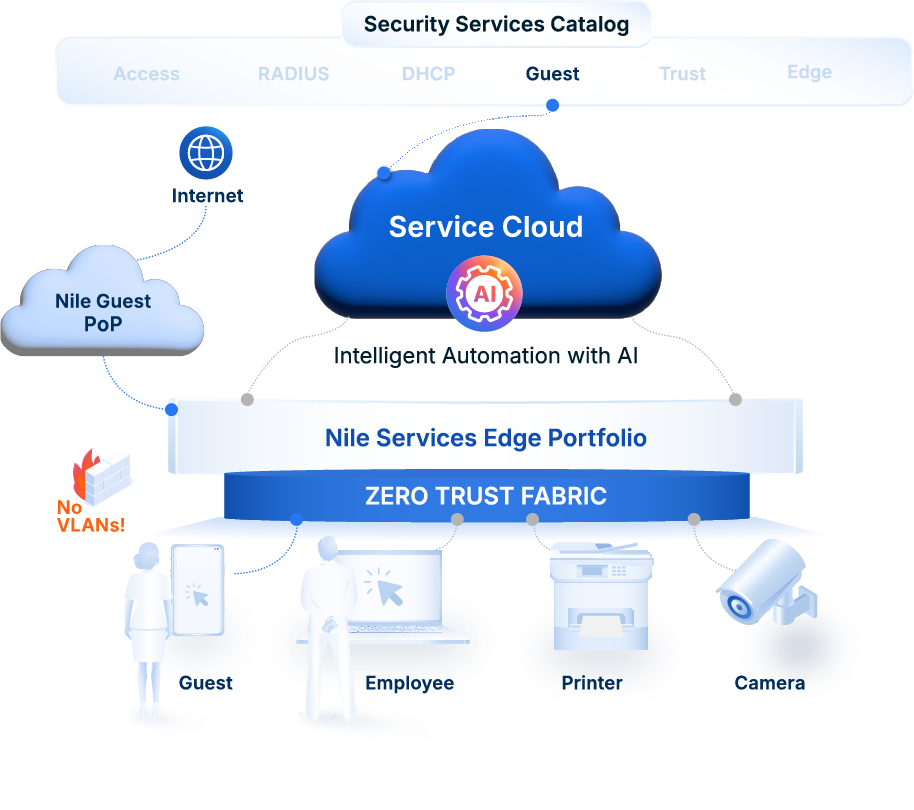
Service Catalog / Guest Service
Industryʼs Only Secure Guest Service
Uncompromising guest access with built-in Zero Trust security
Secure Guest Access, Delivered As-a-Service
All guest traffic isolated and tunneled to a Nile-hosted cloud PoP for ultimate Zero Trust protection.
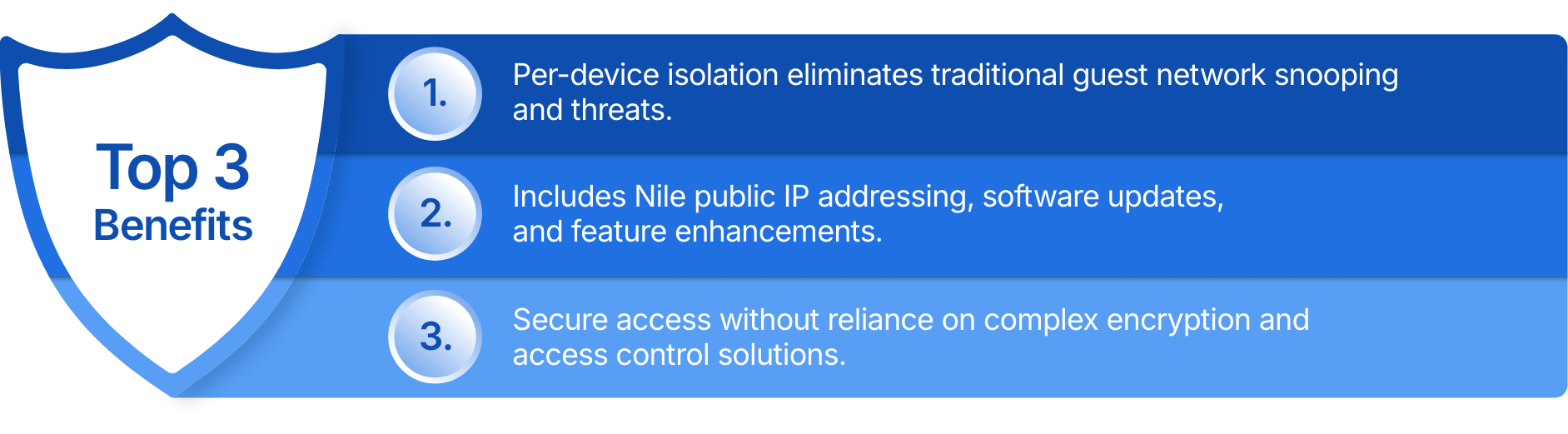
Nile’s Leading-Edge Differentiation
Nile Offers Unmatched IT And Business Advantages
Industry’s most secure, easy-to-use guest solution, without complex add-ons and network changes.
Carta Chooses Guest Service That Exceeds Strict Standards
Leading equity management firm fully isolates guest network from internal network, malware, and prying eyes
“The Nile Guest Service has allowed us to provide internet access to our clients with the confidence that our internal assets and customerʼs data is isolated, helping us exceed internal and external compliance demands.ˮ
Albert Jong,
Senior IT engineer at Carta

Nile Delivers The Industy's Only Secure Guest Access
Nile Makes Securing A Guest Network As Easy As 1, 2, 3
Are You Ready For A Secure Guest Solution?
Download The Industry Solution Brief
Frequently Asked Questions
Why does Nile offer a secondary Guest Service option?
Nile’s add-on Guest Service allows customers to offload existing firewall, NAC, DHCP, and DMZ management requirements. All guest traffic uses Nile provided IP addressing and is directly tunneled to a Nile point-of-presence (PoP) for added security.
What happens once I initiate a Nile Guest Service subscription?
Once signed up, the Guest Service is automatically enabled. The primary Nile point of presence (PoP) is automatically set up. Customers continue to use their own public facing DNS server. IT simply needs to open ports 443 and 6081 outbound on their existing firewalls.
What will users experience when connecting to this Guest Service?
There is no visible difference when connecting to Nile’s more secure Guest Service. Security and simplified management are intended to enhance the experience of IT administrators and those hosting guests.
