Share Via
Zero Trust is one of those ideas that almost every IT leader agrees with in principle. Eliminate implicit trust, restrict lateral movement, and apply policy consistently. Sounds easy, right?
The challenge is that, in legacy networks, Zero Trust has often been layered on in ways that add complexity, including more VLANs, more policies, and more workflows. In the end, that complexity creates more overhead to manage user and device access, mitigate risk, and keep security controls aligned.
The good news is, it doesn’t have to work that way.
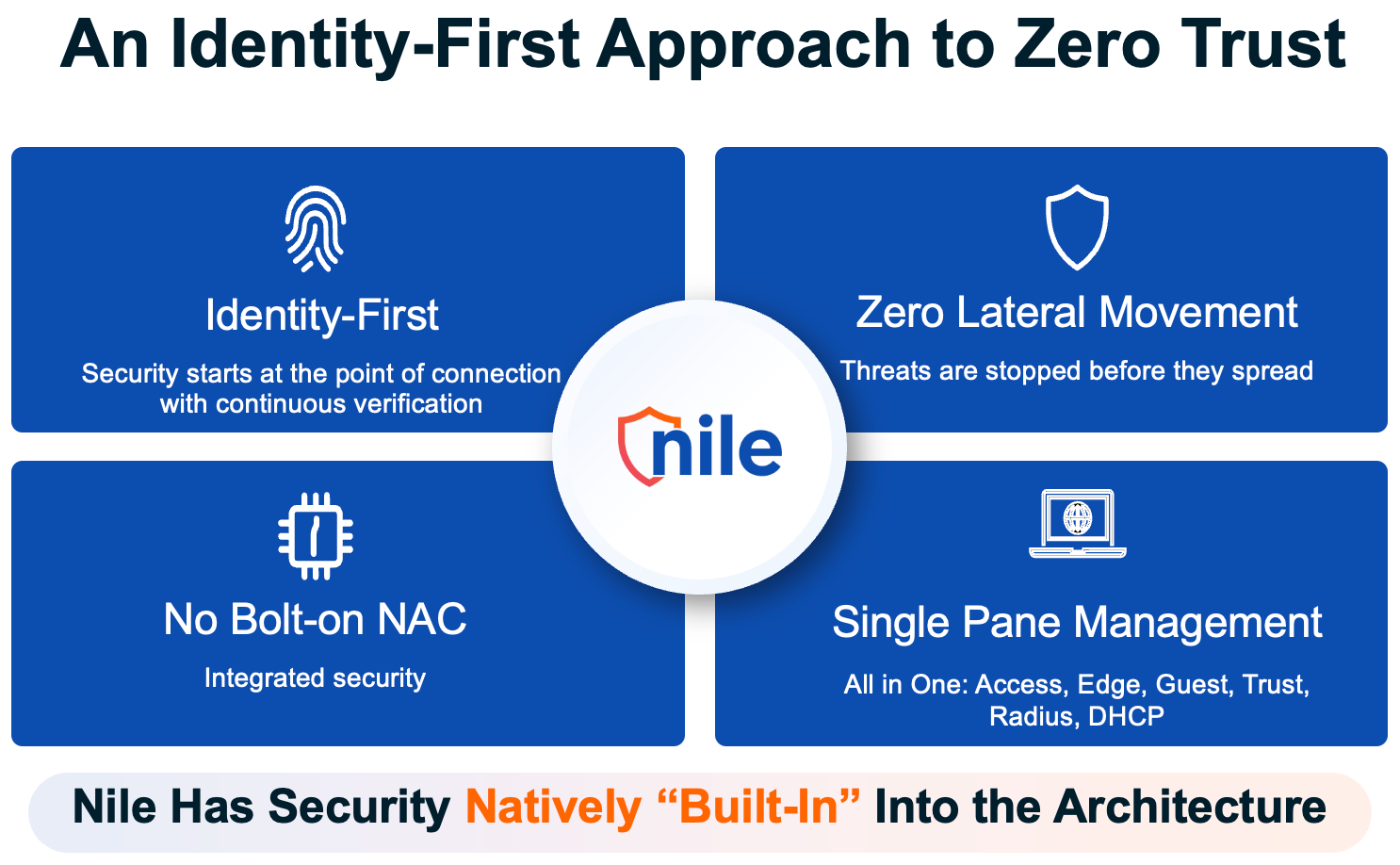
At Nile, we believe security should be stronger and simpler at the same time. That is why we created three short demo videos focused on real Zero Trust security outcomes, not just technical gymnastics and guesswork. Together, they show how organizations can improve security, reduce operational burden, and ultimately get more out of their network with an identity-first approach.
Demo 1: Unified Wired and Wireless Policy Enforcement
One of the biggest operational challenges in enterprise security is maintaining a consistent policy as users and devices connect and move about. On traditional networks, segmentation is often tied to VLANs, subnets, and NAC workflows. That means a user connecting on a wired network may be handled one way, then encounter a different policy path when moving to Wi-Fi or another location.
That creates policy drift, manual work, and troubleshooting overhead.
The Unified Wired and Wireless Policy Enforcement demo highlights a different approach based on unified identity and device context, rather than network location or connection method. On Nile’s Zero Trust Fabric, once connected users and devices retain correct access privileges based on a security policy that works across wired and wireless, regardless of connection method or network location.
The demo also shows how unknown or non-compliant devices can be identified through agentless classification and automatically isolated. There is no need for disruptive VLAN changes, subnet moves, or complicated reauthentication workflows. The result is a more consistent security posture with far less operational effort.
Demo 2: Containing Breaches and Malware
Security teams know that threat prevention is only part of the story. The real test is what happens when a suspicious or compromised device appears on the network.
Too often, containment is messy. Quarantining an endpoint involves placing it in a shared segment, implementing automated network changes that are difficult to manage over time, and occasional manual intervention when things fail. Ultimately, it’s a legacy model that still leaves room for unwanted lateral communication as devices are placed into a VLAN. It’s a process that’s cumbersome, difficult on IT and your users, and increases risk when time matters most.
In the demo, Containing Breaches and Malware, we demonstrate a simpler and more controlled approach to threat containment. Devices that fail health checks are quarantined through policy, without making network changes (as Nile does not use VLANs), readdressing the device, or triggering disruptive network workflows. Because quarantine is not a shared holding area, devices are isolated from one another, helping prevent malware propagation, further reducing the blast radius of a threat, and enabling faster containment with less operational complexity.
Demo 3: Complete Isolation of Guest Users
Guest access is another area where organizations often inherit unnecessary complexity and risk. In traditional environments, guest connectivity requires dedicated VLANs, DHCP scopes, firewall rules, internet policies, and ongoing monitoring for misuse. Even then, unmanaged traffic still traverses enterprise infrastructure in ways that create both risk and operational burden.
In this demo, Complete Isolation of Guest Users, we show how Nile simplifies that model.
When a guest connects using Nile Guest Service, traffic is automatically routed to a secure Nile point of presence (PoP), where DHCP, NAT, and internet breakout are managed with a Nile public IP address. Guest traffic never touches the enterprise network and remains completely isolated from internal resources.
The Nile architecture improves security by design while simplifying operations. IT teams no longer need to build and maintain the traditional sprawl of guest networking infrastructure, yet guests still get fast and trusted access. The result is secure guest connectivity that does not place devices on a shared VLAN, where traffic can be snooped, or worse, and scales across sites without adding operational overhead or unnecessary infrastructure.
Zero Trust Without the Complexity
Taken together, these demos show that Zero Trust need not be more complex to be effective. It should give organizations a more consistent way to enforce policy, a more controlled way to contain threats, and a simpler way to deliver isolated guest access.
This is Nile’s and your advantage. Security is built into the secure fabric itself, not layered on through disconnected tools and operational workarounds. The result is a security model that is easier to operate, faster to respond, and better aligned with the outcomes IT teams actually care about.
If Zero Trust has felt too complex in the past, these demos show there is a simpler, easier path forward to meet both internal and external compliance requirements.
For more on Nile’s Zero Trust Fabric and Secure Service’s Catalog: