Robust wired and wireless that supports today’s evolving indoor and outdoor connectivity demands.
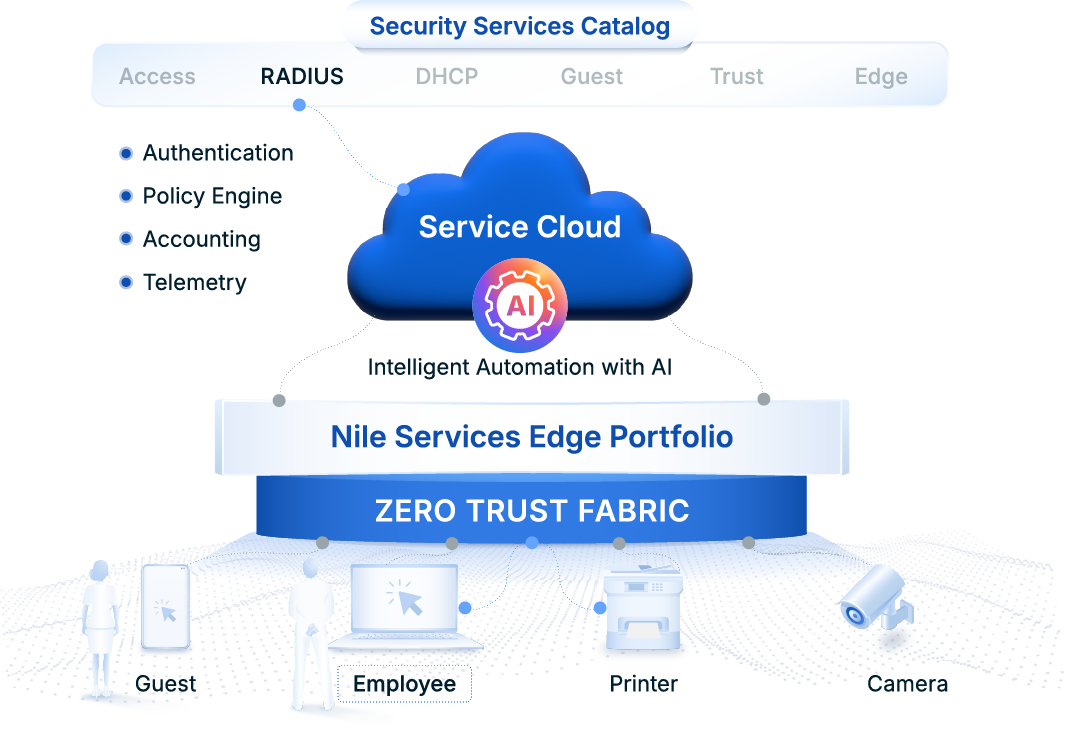
Service Catalog / RADIUS Service
RADIUS Authentication Delivered As-A-Service
Strong security for IT-managed endpoints, BYOD, and IoT
Smarter, Simpler, Secure Device Authentication
A secure-by-design approach that leverages Zero Trust embedded into the network.
Nile's Leading-Edge Differentiation
Nile Offers Unmatched Authentication and Operational Advantages
Nile RADIUS Delivers 50% IT Resource Boost
For a large technology company, a complex 3rd-party NAC solution for primarily device authentication no longer made sense. Nile's secure add-on service eliminated difficult to maintain security policies, and costly time-consuming lifecycle operations.
“With Nileʼs RADIUS Service, we no longer need to manage NAC infrastructure and troubleshoot site-specific authentication issues. Policy enforcement is centralized and tightly integrated—freeing up over 50% of the operational effort previously spent on NAC operations.ˮ
Director of IT
Nile Delivers Strong Authentication Without Complexity
Nile Makes RADIUS As Easy As 1, 2, 3
Ready For A Better RADIUS Service?
Download Solution Brief
Frequently Asked Questions
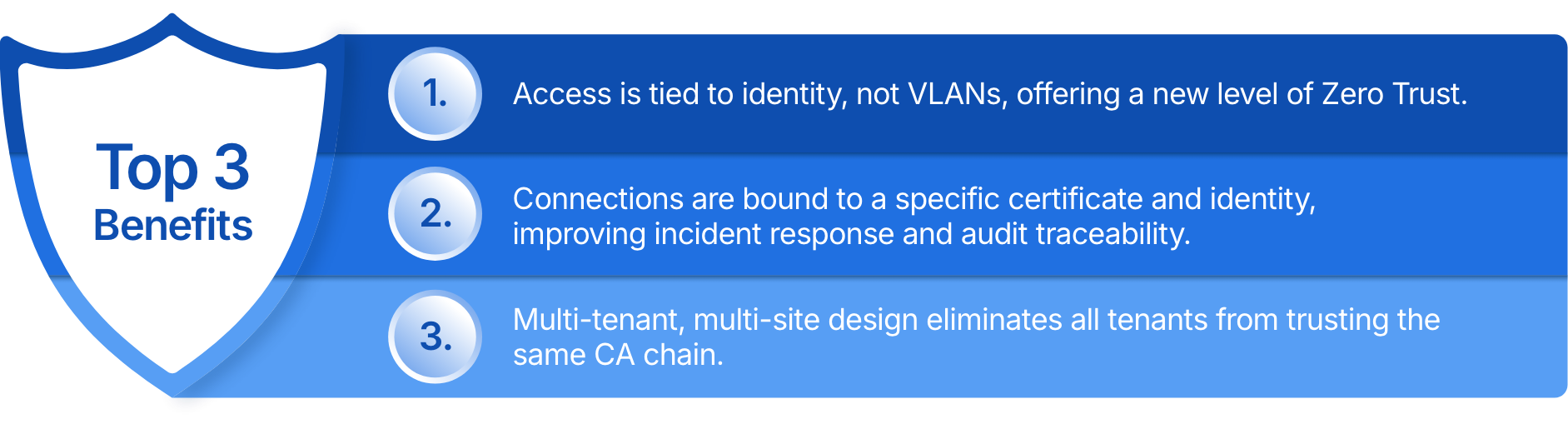
How does Nile RADIUS add to your Zero Trust posture?
In addition to an easier solution to manage, Nile customers can take advantage of our RADIUS service’s integrated Zero Trust Fabric features, such as per-device isolation, built-in authorization and policy creation, device fingerprinting, colorless ports, and a single point of management.
Can Nile RADIUS be used in non-Nile environments?
No. The Nile RADIUS Service is designed to exclusively operate with the Nile Access Service and our ZTF infrastructure as it utilizes and works with Nile’s Cloud and Zero Trust Fabric.
Does Nile handle the distribution of Certificates onto endpoint devices?
No. Nile’s customers will continue to use their existing Certificate Authority (CA) to distribute and update certificates, such as Windows Servers and Group Policy Objects (GPOs) or MDM services such as Microsoft Intune.
