Share Via
Recent academic research presented at NDSS 2026, describes why the AirSnitch vulnerability has generated urgency across the industry regarding Wi-Fi security in legacy networks. In essence, AirSnitch exposed inherent flaws tied to Layer-2 trust and client isolation features.
To understand why traditional networks are vulnerable—and why Nile’s architecture is immune —we need to look beneath the surface. This technical breakdown explores specific attack primitives AirSnitch leverages and how Nile’s Zero Trust Fabric neutralizes an attack.
The AirSnitch Attack Model
It is important to understand that AirSnitch is not a casual Wi-Fi hack; it requires insider access, the simultaneous use of multiple NICs, and favorable network conditions. In short, it is a highly complex attack.
If these conditions are met on a traditional legacy network, the attacker can bypass Wi‑Fi client isolation by exploiting what the researchers’ term “cross-layer identity desynchronization.” In a traditional network stack, a client’s Wi-Fi session keys (Layer 1/2), MAC address (Layer 2), and IP address (Layer 3) are not strictly bound together. Because these layers operate with a degree of implicit trust, attackers can spoof or manipulate identifiers at one layer to bypass isolation mechanisms at another.
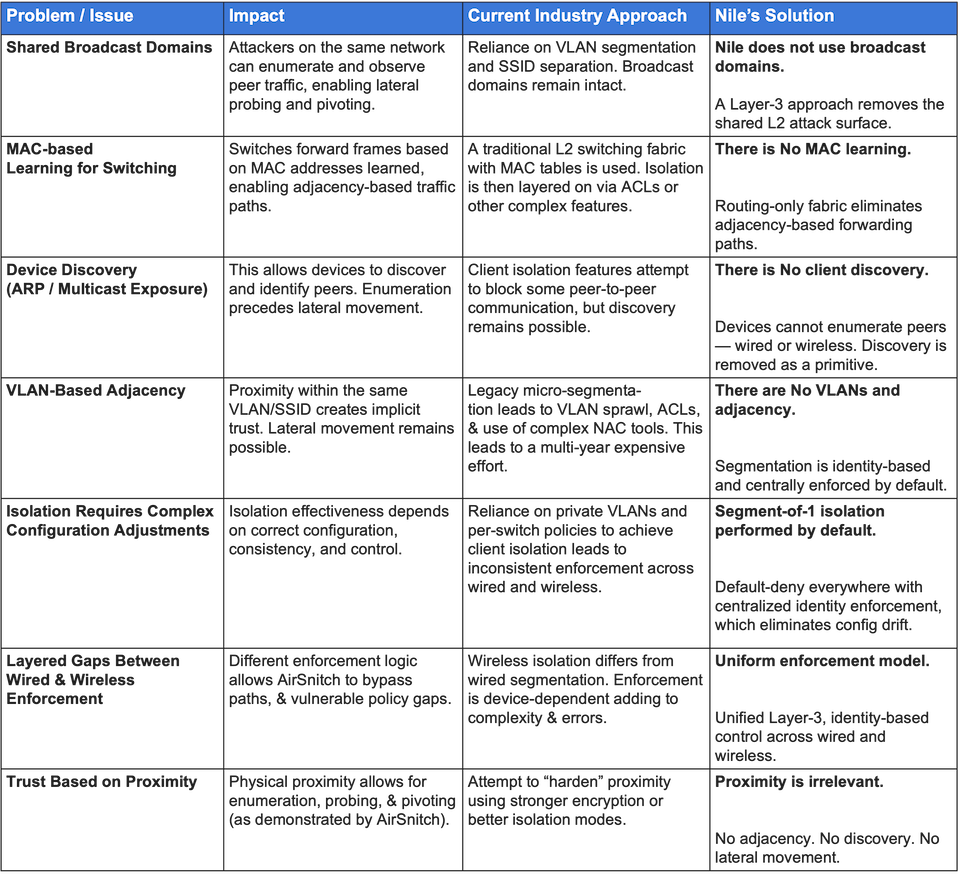
Nile’s Approach Is To Neutralize Legacy Network Vulnerabilities
Before examining specific exploits, the table below illustrates the foundational differences between how traditional networks attempt to manage these risks, and the steps Nile has taken to deliver a better, safer option.
How Nile’s Zero Trust Fabric Combats Airsnitch Vulnerabilities
The following describes how AirSnitch exploits cross-layer identity desynchronization in legacy networks, and how Nile’s architecture structurally blocks each path.
1. AirSnitch Primitive: Uplink Hijack via Spoofed Gateway MAC
How AirSnitch works: By spoofing the gateway’s MAC address, an attacker can trick the network into sending uplink traffic from multiple clients to the attacker first. The attacker then relays this traffic onward, enabling the interception of control and infrastructure traffic like RADIUS or DHCP, printed documents, video stream from camera to server.
Nile’s Defensive Measure: Uplink MitM is impossible In a Nile environment, as preconditions for this attack simply do not exist.
- No AP Bridging: APs do not bridge to the router; instead, every wired and wireless endpoint is tunneled directly to the Zero Trust Fabric (ZTF) Gateway. The AP acts purely as a tunnel endpoint, not a shared Layer-2 switch carrying the router MAC.
- Centralized L3 Gateway: Nile’s ZTF Gateway operates as the Layer-3 gateway, with the gateway MAC securely anchored locally rather than being “movable” behind a wireless port.
- The Result: If a client attempts to spoof the default gateway’s MAC, the AP still tunnels the frame to the Nile ZTF Gateway, which forwards the packet to the destination based on IP address, not to the attacker device. There is no mechanism for “gateway MAC → attacker port” rebinding, meaning victim uplink traffic cannot be redirected.
2. AirSnitch Primitive: Downlink Hijack via Port Stealing
How AirSnitch works: This is an adaptation of classic Ethernet port-stealing. The attacker associates on another virtual BSSID (like a guest SSID or a different band) using the victim’s MAC address. The AP or distribution switch updates its MAC-to-port mapping, causing downlink frames intended for the victim to be sent to—and encrypted for—the attacker.
Nile’s Defensive Measure: We prevent desynchronization via authoritative binding In a Nile fabric. This classic port-stealing attack is quickly contained and effectively neutered because cross-layer desynchronization is not permitted:
- Single Authoritative Binding: When a client joins the Nile network, its context is strictly bound to the mac address, an authenticated session and segment at the Gateway. Layers 2 and 3 are intrinsically linked to the authenticated identity.
- Immediate Conflict Resolution: Because Nile maintains exactly one valid binding, any competing attachment for the same MAC forces a conflict resolution. This results in the flagging an anomaly and preventing a silent “invisible” MitM hijack.
- Active Detection: Nile’s AP and Gateway logic includes native MAC-spoofing detection. Suspicious MACs appearing from multiple radios or with inconsistent contexts can be immediately blocked or quarantined.
3. AirSnitch Primitive: Gateway Bouncing
How AirSnitch works: The attacker sends packets addressed to the default gateway’s MAC, but uses the victim’s IP address. The goal is to force the Layer-3 gateway to route traffic between clients, entirely bypassing Layer-2 client isolation features.
Nile’s Defense Measure: Segment-of-1 isolation is inherent to Nile’s Zero Trust Fabric and renders gateway bouncing useless.
- Default-Deny Policy: Nile’s fabric is pure Layer-3 with segment-of-1 and default-deny policies natively enforced.
- No Generic Routing: Client-to-client IP connectivity is not allowed by default. Flows are steered to our built-in policy engine or SSE/firewalls or specific services based on identity, rather than being simply routed between two endpoints on a common subnet.
- The Result: A “bounce” packet sent from an attacker will hit Nile’s Zero Trust policy engine and be dropped, preventing it from being blindly returned to the victim. Nile Gateways do not act as generic Layer-3 client-to-client routers.
The Bottom Line
The ultimate lesson learned is that traditional architectures that treat SSIDs, VLANs, and client isolation settings as separate security boundaries are fundamentally broken, leaving organizations knowingly vulnerable.
Nile replaces the legacy architecture with a true Zero Trust implementation and segment-of-1 design, making AirSnitch a non-factor. Spoofing a victim’s MAC or manipulating gateways in a Nile ZT Fabric does not yield a clean, persistent attack surface; it results in denied access, blocked MAC addresses, and dropped packets.
- For more on AirSnitch
- Nile Trust Service overview