Share Via
The Data Is Clear: The Campus Remains the Easiest Place to Break In
Enterprise security discussions today often focus on cloud workloads, identity platforms, and secure access architectures. Those areas matter, but the data behind real-world breaches points to a consistent structural weakness inside the enterprise environment itself.
Several independent sources highlight a recurring pattern:
- The Human Element: Roughly 68% of breaches involve credential theft, phishing, or human error.
- Lateral Expansion: Incident response investigations consistently show that lateral movement is a defining stage of major intrusions.
- A Visibility Gap: Analysts estimate that more than 80% of devices connected to enterprise networks are IoT or operational systems not directly managed by IT.
- Infrastructure as-a-Target: A growing portion of vulnerabilities now target network infrastructure itself, not just endpoints or applications.
Individually, these points are well understood. Together, they tell a clear story: attackers do not need sophisticated entry points. They compromise the weakest reachable device and then move laterally across the environment. What determines the impact of a breach is not how the attacker gets in, but how far they can move once they are inside.
This is where the campus network becomes critical. The the wired and wireless network inside offices, hospitals, warehouses, factories, and retail locations that connects users, devices, and systems directly to one another. It is often where lateral movement becomes possible. Unfortunately, the campus was never designed with that threat model in mind.
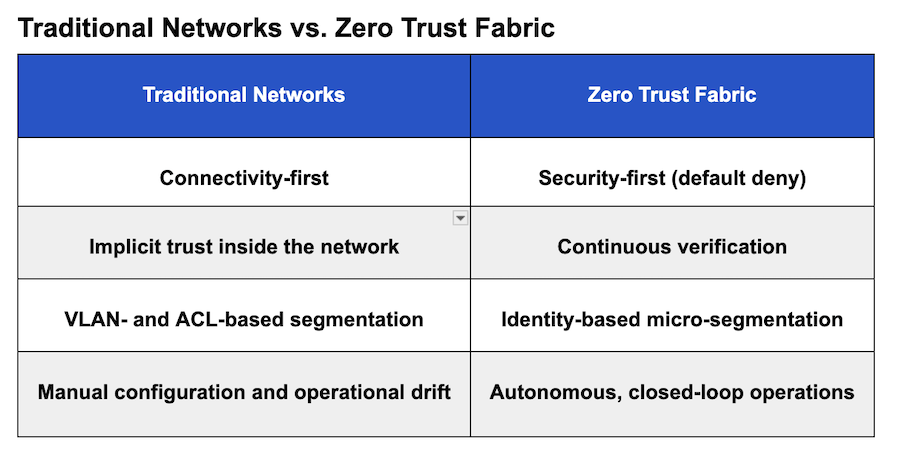
For decades, the industry focused on connectivity, making communication possible, and adding security later. Firewalls, VLANs, and NAC systems were introduced over time to address emerging risks. Each solved a problem. But the architecture remained the same. The network was built to communicate first, with security layered on afterward.
The Structural Gap: Where Traditional Networks Break
Traditional campus networks were never designed to operate under a “breach assumed” model. As a result, the same issues appear consistently across environments:
- Admission is not enforcement: NAC systems verify identity at the point of connection, but once a device is admitted, trust is typically assumed to persist.
- The segmentation illusion: VLANs organize traffic, but devices within the same segment can still communicate freely, allowing lateral movement.
- The IoT/OT blind spot: Embedded devices often cannot run endpoint agents or support sophisticated authentication, leaving large portions of the network unmanaged.
These are not isolated problems. They are architectural consequences of how the network was originally designed. The network is optimized for reachability, while security is expected to limit that reachability through overlays and bolted-on controls. To compensate, organizations introduce increasing complexity—PVLANs, dynamic VLANs, dynamic ACLs, overlay NAC systems, and firewall-based segmentation. Each adds control, but also adds operational overhead and drift. The underlying issue remains unchanged: the network still allows communication by default.
Enter the Zero Trust Fabric: Security as an Inherent Property
A Zero Trust fabric is not a collection of controls layered onto the network. It is an architecture where security is built into how the network operates.
Default Deny by Design
Instead of configuring a network to behave securely, the fabric operates with a default-deny posture from the start. Every device is isolated, and communication is allowed only when explicitly authorized by policy.
The Segment of OneThis is enforced through Layer 3 host-based isolation, often described as a segment of one. Devices do not share a broadcast domain, eliminating Layer 2 adjacency and preventing lateral movement by design.
Access is defined by identity, not by VLAN, IP address, or physical location. Whether a device is connected via a wired port or Wi-Fi, its policy remains consistent.
Inherently Hardened Infrastructure
The infrastructure itself is inherently hardened. All elements of the network mutually authenticate, establishing a secure chain of trust. Traffic is encrypted in transit, eliminating implicit visibility and reducing the attack surface within the network.
Deterministic and Autonomous
What makes this model practical at scale is the underlying deterministic architecture. There are no VLANs to design, no complex ACLs to maintain, and no per-site tuning of ports, radios, or protocols. The network behaves consistently across environments, eliminating snowflake designs and reducing variability.
Through closed-loop automation and agentic operations, the system continuously validates its state, monitors behavior, and enforces policy in real time. This removes dependence on manual configuration and prevents the configuration drift that undermines traditional architectures.
The Architectural Question
Most Zero Trust initiatives begin with identity systems, endpoint security, or cloud-delivered controls. These are important components of a modern security architecture. But before any of them can succeed, a more fundamental question must be asked:
Is your underlying network architecture designed to enforce Zero Trust—or to work around it?
If the architecture still assumes connectivity first, security will always be compensating for that assumption. And attackers will continue to exploit it.
Learn More: