Robust and modern wired and wireless that supports today’s evolving indoor and outdoor connectivity demands.
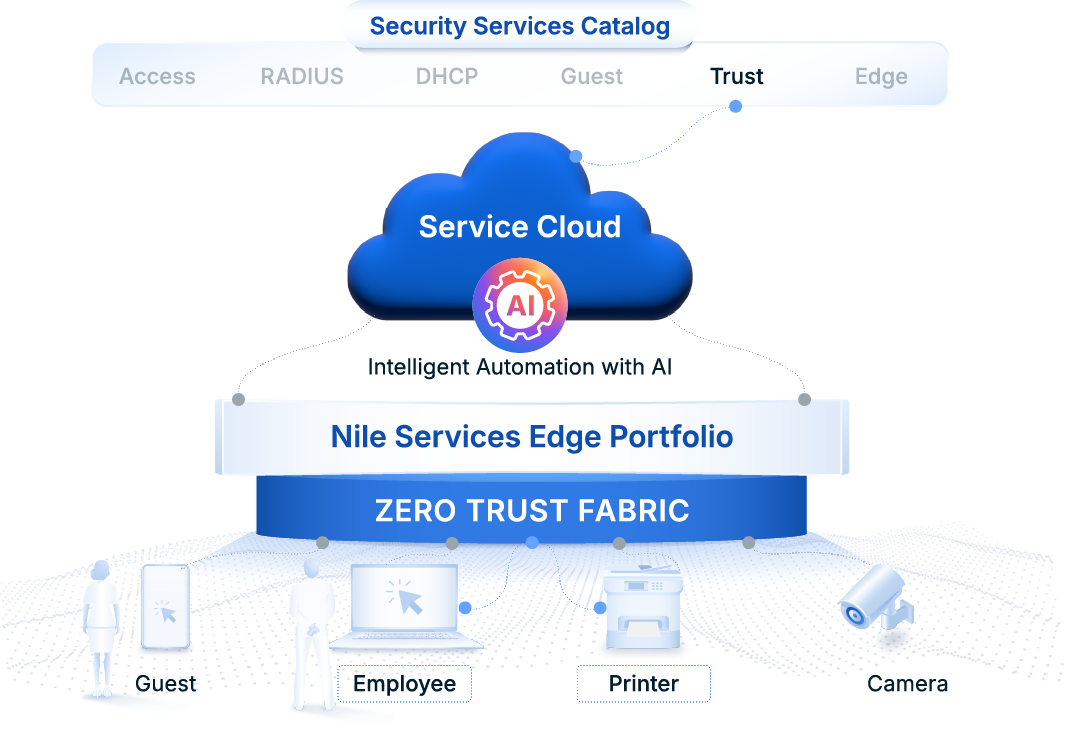
Service Catalog / Trust
Advanced Security For Campus And Branch
Datacenter-Class Features That Reduce Breaches And Lower Risk
Zero Trust You Can Trust
Built-in security that eliminates disparate infrastructure deployment, complexity and high costs.
Nile’s Leading-Edge Differentiation
Nile Offers Unmatched Security And Compliance Advantages
University Contains Threats And Risk With Nile Zero Trust
Nileʼs Zero Trust Fabric natively offers a high degree of protection that extends from students and staff, to visitors and IoT. Embedded security and autonomous operations curtailed traditional network risks that threatened the institutions’ financial stability and reputation.
“Nile configured our network to eliminate the risk of cross-horizontal connections and lateral movement. Devices are now individualized and placed into a segment-of-one with connections to the firewall and Internet, meaning users can’t take advantage of a flat network.”
Jonathan Breitbarth
Director of Computer Services

Nile Delivers Industry's Only Zero Trust LAN Network
Nile Makes Achieving Zero Trust Compliance As Easy As 1, 2, 3
Ready For Next-gen Security You Can Trust?
Download Solution Brief
Frequently Asked Questions
How is Nile's Trust Service different from legacy network solutions?
Traditional networks typically rely on VLANs, overlays, and external enforcement tools to provide security. IT teams are then forced to buy and piece everything together in order to close security gaps inherent to decades old vulnerabilities.
Do I still need separate NAC and microsegmentation solutions?
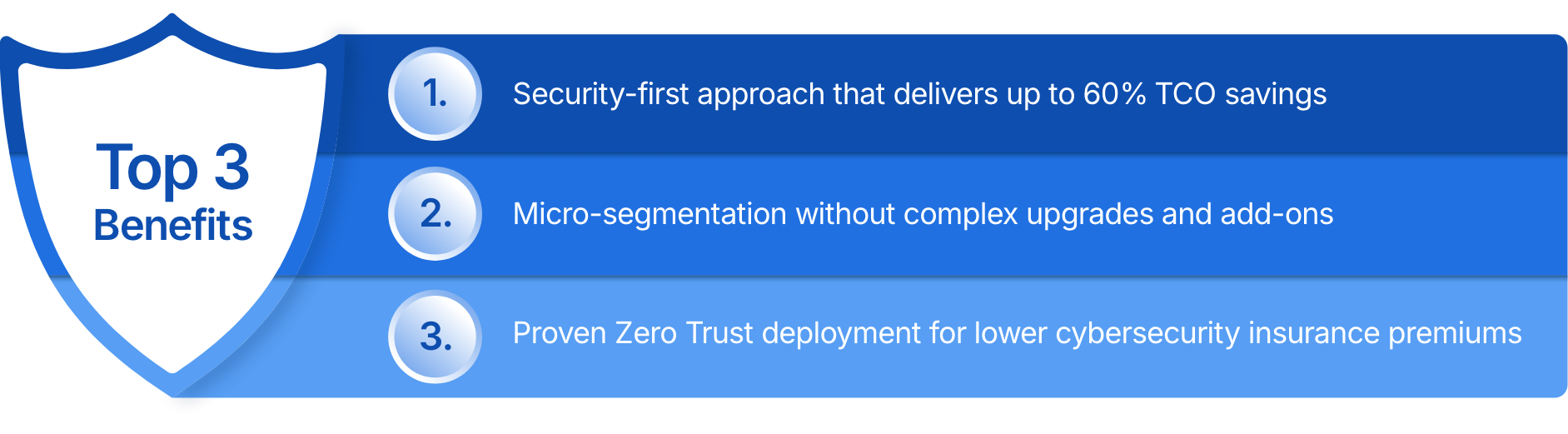
No, in most cases. Traditional NAC and other add-on solutions are replaced to deliver secure, default-deny access and microsegmentation without complex NAC appliances, VLAN sprawl, VxLAN complexity, and external policy servers.
How does Trust Service secure IoT and other unmanaged devices?
The use of segment-of-one default host-based isolation, agentless identification, and policy-based access control ensures that these devices are only permitted to communicate with explicitly authorized resources based on least-privilege policies, limiting lateral movement and blast radius of potential threats.
